Microsoft has released security updates for flaws in Exchange Server 2013, 2016, and 2019 and has warned admins to immediately patch a high severity Exchange Server vulnerabilities as soon as possible.
Earlier this year, the Beijing-backed hackers (also known as Hafnium) exploited on-premises Exchange server software vulnerabilities. Microsoft now warns that patches, while helpful, may not be enough to thwart future attacks.
The updates were released as part of Microsoft’s November 2021 Patch updates for Windows, the Edge browser, the Office suite, and other software products. Four vulnerabilities were exploited and one of the new patches (CVE-2021-42321) is under attack.
Microsoft notes that these vulnerabilities affect on-premises Microsoft Exchange Server but that Exchange Online customers are protected.
What makes this challenging is that attacks which occur after user authentication can have legitimate but stolen credentials. The Beijing attackers accessed Exchange Servers post-authentication through the four bugs or via stolen credentials. From here they could create web shells to communicate with an infected computer. The real issue is that these shells need to be manually removed because they can survive on a system even after a patch.
Although two-factor authentication won’t fully protect against attackers exploiting the new Exchange flaws, it can make it more challenging to get through. Once a two-factor account has been compromised though it is irrelevant.
What does this mean for you?
If you are running Exchange server versions 2013, 2016, or 2019 you will need to address these vulnerabilities. Microsoft says the vulnerability doesn’t affect Exchange online, with the exception of on-premise hybrid servers.
Dustin Childs, with Trend Micro’s Zero-Day Initiative, noted, “As with all Exchange bugs in the wild, we urge Exchange admins to test and deploy the patches as soon as possible”.
What should you do about it?
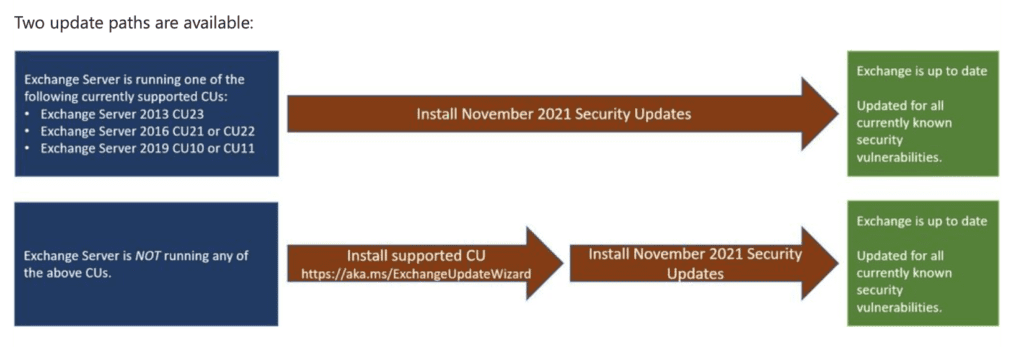
Microsoft recommends running the PowerShell query on your Exchange server to detect compromises and admins are encouraged to update to one of the supported CUs and follow detailed instructions from Microsoft.
If you want to check and see if any of your Exchange servers were hit by these exploitation attempts, you can run the following PowerShell query on each Exchange server to check for specific events in the Event Log:
Get-EventLog -LogName Application -Source “MSExchange Common” -EntryType Error | Where-Object { $_.Message -like “*BinaryFormatter.Deserialize*” }
If any events are returned by this command, you should contact Microsoft to report the problem and seek assistance.